SCADA Networks and NERC CIP Compliance
In the world of utility operations, cybersecurity and compliance are no longer optional — they are essential. Yet, a common myth persists among smaller utilities and co-ops: “SCADA networks don’t really need to meet NERC CIP standards — those rules only apply to the bulk power system.”
This belief, while understandable, is increasingly outdated and risky. As the energy landscape evolves, the expectations for cybersecurity and compliance are cascading down from transmission systems to distribution-level networks. In this article, we’ll explore the origins of this myth, the realities of NERC CIP compliance for distribution utilities, and how a practical approach like “CIP Lite” can help smaller utilities strengthen their SCADA networks without overburdening their resources.
The Origins of the Myth
The misconception that SCADA networks at the distribution level are exempt from NERC CIP standards stems from the original intent of the regulations. NERC CIP (Critical Infrastructure Protection) standards were initially designed to secure the bulk power system — the high-voltage transmission networks that form the backbone of the electric grid.
Because smaller utilities and co-ops typically operate at the distribution level, many assumed that these standards didn’t apply to them. However, as the grid becomes more interconnected and distributed energy resources (DERs) proliferate, the lines between transmission and distribution are blurring. This shift has brought new scrutiny to distribution networks, particularly their cybersecurity practices.
The Reality: CIP Expectations Are Cascading Down
While not every co-op or municipal utility is directly registered with NERC, the influence of CIP standards is expanding. Here’s why distribution utilities can no longer afford to ignore these requirements:
1. Audit Risk: Even if a utility is not formally registered with NERC, it may still be required to demonstrate security practices when interconnected with CIP-covered systems. For example, larger investor-owned utilities (IOUs) or regional transmission organizations (RTOs) may request evidence of cybersecurity measures to ensure the security of their own networks.
2. Cybersecurity Liability: SCADA networks are prime targets for cyberattacks, including ransomware, grid disruptions, and data breaches. A single vulnerability in a distribution network can have cascading effects, potentially impacting the broader grid. CIP-aligned best practices help mitigate these risks and protect critical operations.
3. Regulatory Expansion: The scope of NERC CIP standards is broadening to include distributed energy resource (DER) interconnects, renewable energy systems, and distribution-level operational technology (OT) networks. As these systems become more integral to grid operations, they are increasingly subject to regulatory oversight.
4. Customer and Partner Expectations: Larger IOUs, RTOs, and independent system operators (ISOs) are raising the bar for their distribution partners. Even if compliance isn’t mandated, these organizations expect smaller utilities to follow CIP-aligned practices to ensure the security and reliability of interconnected systems.
What is CIP Lite?
For smaller utilities and co-ops, full NERC CIP compliance can be overwhelming and resource-intensive. That’s where “CIP Lite” comes in. Strictly speaking, “CIP Lite” is not an official NERC standard. Instead, it’s an industry term used to describe a scaled-down approach to implementing the most critical CIP cybersecurity controls. It provides a practical framework for smaller utilities to strengthen their SCADA networks without the complexity and cost of full compliance.
Core Focus Areas of CIP Lite
CIP Lite focuses on the following key areas:
- Secure Remote Access: Implementing multi-factor authentication (MFA), virtual private networks (VPNs), and logging to protect remote connections.
- Network Segmentation: Separating operational technology (OT) and information technology (IT) networks using technologies like MPLS and Virtual Routing and Forwarding (VRF).
- Critical Device Inventory and Patching: Maintaining an up-to-date inventory of critical devices and ensuring timely software updates to address vulnerabilities.
- Event Monitoring and Incident Response: Establishing systems to monitor network activity, detect anomalies, and respond to security incidents.
By focusing on these areas, CIP Lite provides smaller utilities with a credible, cost-effective way to enhance cybersecurity and align with industry best practices.
How MPLS and LTE Enable CIP Lite
MPLS (Multiprotocol Label Switching) and LTE/Private LTE technologies are critical enablers of CIP Lite, offering the tools needed to secure SCADA networks and meet evolving compliance expectations.
- Segmentation with VRFs: MPLS allows SCADA, AMI (Advanced Metering Infrastructure), voice, and IT traffic to coexist securely on a single converged network. Virtual Routing and Forwarding (VRF) instances ensure that each type of traffic is isolated, preventing unauthorized access and ensuring performance. LTE and Private LTE extend this segmentation to remote substations, intelligent electronic devices (IEDs), and pump stations.
- Deterministic QoS: MPLS ensures low latency and reliability by prioritizing teleprotection and SCADA traffic. LTE/Private LTE extends secure, high-priority connectivity to rural and remote sites, ensuring critical applications remain operational.
- Visibility and Control: MPLS provides per-service monitoring and logging, enabling utilities to track network activity and detect potential threats. LTE/Private LTE extends this visibility to the edge, supporting CIP Lite’s event-tracking requirements.
- Resiliency: MPLS Fast Reroute (FRR) ensures network reliability with failover times under 50 milliseconds. LTE/Private LTE adds redundant access paths, ensuring continuous connectivity even in the event of a failure.
By combining MPLS with LTE/Private LTE, co-ops can implement CIP Lite end-to-end, from the network core to the field, without overbuilding or overspending.
MCA’s Role in CIP Lite Implementation
At MCA, we understand the unique challenges faced by co-ops and municipal utilities. That’s why we specialize in designing and deploying CIP Lite architectures that strengthen SCADA security and operational resilience.
Our Solutions Include:
- MPLS/VRF Segmentation: Securely separate SCADA traffic from corporate IT networks.
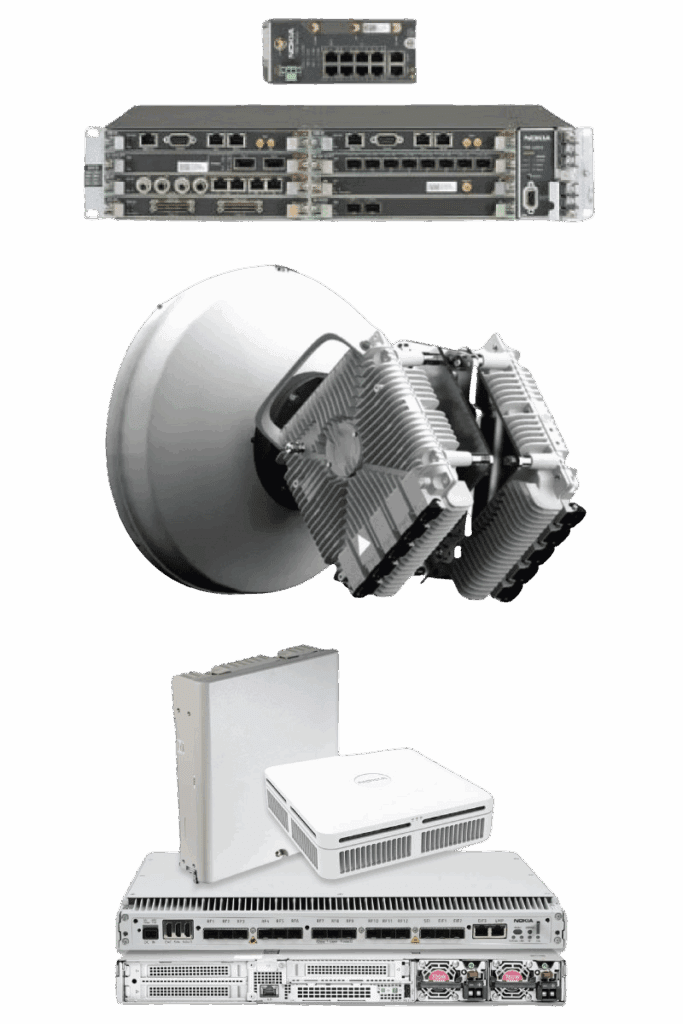
- Nokia 7705 SARs: Deploy routers with built-in CIP security features for robust protection.
- Licensed Microwave and Fiber Backhaul: Ensure secure, high-capacity transport for OT isolation.
- Private LTE/LTE Integration: Extend secure connectivity to remote SCADA and DER assets.
- Lifecycle Support and Documentation: Provide ongoing support and documentation to meet CIP Lite audit expectations.
The Takeaway
SCADA networks may not always fall under mandatory NERC CIP compliance, but aligning with CIP Lite best practices is quickly becoming the industry standard. By adopting CIP Lite, co-ops and municipal utilities can:
- Protect their operations from cyber threats.
- Meet the expectations of larger partners and regulators.
- Prepare for future compliance requirements.
MPLS provides the backbone for secure segmentation, LTE/Private LTE extends secure connectivity to the field, and MCA delivers the expertise and solutions to make it all work seamlessly.
Next Step
Contact MCA today to schedule a 15-minute CIP Lite workshop. Learn how we can help right-size SCADA protections for your utility and prepare your network for tomorrow’s compliance landscape.
Click to Download an Article Summary >>
Article Appendix
Key Industry and Technology Terms
1. SCADA (Supervisory Control and Data Acquisition): A system used by utilities and industrial operations to monitor and control equipment and processes remotely. SCADA is critical for managing power grids, water systems, and other infrastructure.
2. NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection): A set of standards designed to secure the assets required for operating North America’s bulk electric system. These standards focus on cybersecurity, physical security, and operational reliability.
3. CIP Lite: An industry term used to describe a scaled-down approach to implementing the most critical NERC CIP cybersecurity controls. CIP Lite is designed for smaller utilities and co-ops that are not required to meet full CIP compliance but still need to enhance their cybersecurity practices.
4. Bulk Power System: The high-voltage transmission network that forms the backbone of the electric grid, responsible for delivering electricity over long distances.
5. Distribution Network: The lower-voltage portion of the electric grid that delivers electricity from substations to homes, businesses, and other end users.
6. DER (Distributed Energy Resources):
Small-scale power generation or storage technologies, such as solar panels, wind turbines, or batteries, that are connected to the grid and can operate independently or in coordination with the grid.
7. MPLS (Multiprotocol Label Switching): A high-performance network protocol that directs data from one node to the next based on short path labels rather than long network addresses, enabling faster and more efficient data routing.
8. VRF (Virtual Routing and Forwarding): A technology that allows multiple virtual routing tables to coexist on the same physical router, enabling secure traffic segmentation for different applications like SCADA, IT, and voice.
9. LTE (Long-Term Evolution): A wireless communication standard used for high-speed data transmission over public or private cellular networks. Private LTE networks are often deployed by utilities to provide secure, reliable connectivity for remote sites.
10. Private LTE: A dedicated LTE network owned and operated by an organization, such as a utility, to provide secure and reliable wireless communication for critical applications.
11. Secure Remote Access: A cybersecurity practice that ensures only authorized users can access a network remotely. It typically involves technologies like multi-factor authentication (MFA), virtual private networks (VPNs), and activity logging.
12. Network Segmentation: The practice of dividing a network into smaller, isolated segments to improve security and performance. For example, separating SCADA traffic from IT traffic ensures that a breach in one segment does not affect the other.
13. Deterministic QoS (Quality of Service): A network feature that prioritizes specific types of traffic, such as SCADA or teleprotection, to ensure low latency and high reliability for critical applications.
14. Fast Reroute (FRR): A feature in MPLS networks that quickly redirects traffic to an alternate path in the event of a failure, typically within 50 milliseconds, ensuring minimal disruption.
15. Critical Device Inventory: A comprehensive list of all devices that are essential to a utility’s operations, including SCADA systems, routers, and IEDs. Maintaining this inventory is a key component of CIP Lite.
16. Event Monitoring: The process of tracking and analyzing network activity to detect anomalies, potential threats, or security incidents.
17. Incident Response: A structured approach to addressing and managing cybersecurity incidents, including identifying the issue, containing the threat, and restoring normal operations.
18. Licensed Microwave: A wireless communication technology that uses licensed frequency bands to provide high-capacity, low-latency connectivity, often used for utility backhaul networks.
19. Fiber Backhaul: The use of fiber-optic cables to transport data from local networks to a central network or data center, offering high bandwidth and low latency.
20. RTO (Regional Transmission Organization): An independent entity responsible for managing the transmission grid and ensuring reliable electricity delivery across a specific region.
21. ISO (Independent System Operator): Similar to an RTO, an ISO oversees the operation of the electric grid and wholesale electricity markets in a specific area.
About MCA
We believe every workplace should be safe, secure, and efficient. As trusted advisors, we deliver integrated communication, connectivity, and security solutions with a Service First mindset – driven by a team that cares deeply about our customers and each other.
Why MCA? At MCA, we help solve critical communication, connectivity, and security challenges with turnkey, integrated system solutions—from two-way radios and in-building wireless to video surveillance, access control, and more. MCA is built from over 50 companies with deep technical expertise and strong local roots. And we’re still growing—expanding our capabilities, our reach, and our team.
Our 100+ Solution Centers bring together sales, installation, service, and customer operations teams to deliver seamless, nationwide support. Guided by our Service First value, we don’t just connect the wires and walk away—we provide customized solutions backed by deep expertise and lifecycle support.


