Home » Security Solutions » Access Control Systems » ACMS, ACaaS, & VMS Software » On-Premise Access Control Management Systems

For organizations that demand complete control and ownership of their physical security infrastructure, On-Premise Access Control Management (ACM / ACMS) solutions are the ideal choice. These systems offer local data storage, direct network access, and full configurability, making them well-suited for industries such as government, healthcare, education, corporate campuses, and critical infrastructure. In environments where regulatory compliance, uptime reliability, and data sovereignty are critical, on-premise ACM provides unparalleled advantages.
Modern on-premise ACM systems deliver advanced features like robust credential management, comprehensive audit trails, real-time access decision-making, and seamless integration with video surveillance, intrusion detection, and building management systems. At MCA, we provide powerful on-premise access control platforms that are secure, scalable, and fully customizable to align with your organization’s operational needs and risk management strategies.
On-Premise Access Control Management platforms are locally hosted solutions designed to manage credentials, access permissions, schedules, and door activity within a secure internal network. These systems ensure complete control over access events and identity management, delivering uninterrupted operation, enhanced cybersecurity, and compliance with internal governance standards.
Unlike cloud-based models, on-premise ACM systems eliminate reliance on external servers or internet connectivity. This provides organizations with full data control, high availability, and immediate responsiveness. With enterprise-grade scalability, role-based access policies, and native integration with on-site video management systems (VMS) and alarm platforms, on-premise ACM empowers organizations to strengthen perimeter security, streamline access operations, and maintain compliance while safeguarding system integrity.

Avigilon Unity Access is a secure and scalable on-premise ACMS designed for organizations that demand complete control over their access infrastructure. Hosted within your own network, it enables robust credential management, alarm monitoring, and policy enforcement without dependency on external cloud services. Perfect for sectors like government, healthcare, and education, Unity Access ensures uninterrupted access control, regulatory compliance, and seamless adaptability.
Unity Access features a streamlined, intuitive interface accessible through any browser within your network. Security personnel can effortlessly manage doors, permissions, and alarms without the need for additional client software. Its built-in mobile accessibility allows authorized users to monitor and respond to access events in real time, even while away from their desks, ensuring flexibility and efficiency.
Unity Access is built on a custom Linux distribution, offering a secure and resilient foundation that reduces attack surfaces and minimizes maintenance requirements. Unlike systems that rely on Windows OS, this architecture significantly lowers vulnerability to cyber threats, ensuring operational continuity and reducing the burden of frequent patching while maintaining a secure access control environment.
Unity Access fully integrates with Avigilon Unity Video, providing real-time identity verification and a centralized platform for managing security events. Its open-platform architecture supports third-party readers, door controllers, biometric devices, and RESTful API integrations. This flexibility allows organizations to scale their security infrastructure intelligently, free from vendor lock-in constraints, and to build a system tailored to their unique needs.
Interactive floorplans and maps within Unity Access offer operators enhanced situational awareness by visualizing access activity and managing live alerts. From the command center, security teams can trigger remote lockdowns and respond quickly to unauthorized entries or system anomalies. This functionality empowers teams to make fast, informed decisions during critical incidents to maintain security and safety.
Unity Access supports a broad range of credential options, including printed badges, mobile devices, and biometric authentication. By integrating with Unity Access Verify and third-party MFA tools, organizations can implement advanced identity policies, streamline user onboarding, and ensure secure access assignment. This capability enhances security while maintaining a user-friendly experience for administrators and end-users alike.
Unity Access is designed to meet the needs of organizations of any size, whether managing a single site or thousands of doors. Enterprise and Enterprise Plus appliances support large deployments with up to 4,000 doors and include active failover and database synchronization. Professional models cater to small to medium-sized businesses with support for up to 50 doors, while Virtual Appliance options enable seamless deployment in private cloud or virtualized environments with full compatibility for platforms like vMotion and Hyper-V.

While Avigilon Unity Access remains a premier choice for many of our clients, MCA’s access control portfolio includes a diverse range of enterprise-grade on-premise platforms tailored to meet specific operational needs. Whether your organization prioritizes federal compliance, seamless third-party integrations, or scalability across global sites, our partner ecosystem offers highly configurable, reliable systems designed for any security environment. Below are some of the most trusted alternatives in our lineup.

LenelS2 OnGuard is a scalable, high-performance physical access control system (PACS) built for enterprise campuses, government facilities, and healthcare networks. Supporting up to 10,000 doors and 400,000 cardholders, OnGuard features browser-based credential management, intelligent lockdown protocols, and seamless video integration with Milestone XProtect. Its compatibility with Mercury controllers, biometric readers, and mobile credentials ensures robust, future-ready security.

Milestone XProtect Access is a software extension that seamlessly integrates access control with existing XProtect VMS, unifying video and access operations. Operators can monitor doors, validate identities, and grant access from a single interface, enabling rapid response and streamlined management. Compatible with a wide range of third-party systems, XProtect Access enhances security for enterprises already using Milestone video surveillance.

Genetec Synergis is an IP-based, open-architecture access control platform that unifies access control with video surveillance, license plate recognition, intrusion detection, and identity management through Genetec Security Center. Supporting up to 4,000 doors per system, it features end-to-end encryption, certificate-based authentication, and multi-factor credentialing. With flexible deployment options it delivers secure, adaptable access control for corporate campuses, airports, utilities, and federal facilities.

Bosch's Access Management System (AMS) delivers enterprise-grade access control with intuitive tools and powerful integrations. Supporting up to 10,000 doors, it offers GDPR-compliant encryption, multi-factor authentication, and license plate recognition. With drag-and-drop configuration and integration with Bosch BVMS and third-party systems, AMS is ideal for offices, industrial sites, and parking infrastructures prioritizing security and compliance.

ACRE DNA Fusion is a robust open-platform access control solution for real-time automation and seamless integrations. It centralizes management across facilities with advanced dashboards, credential management, and alarm integration. Compatible with Mercury, Hanwha, HID, Allegion, and Assa Abloy hardware, it provides high security and scalability without vendor lock-in. Its web and mobile interfaces enable remote management and seamless integration with software like Milestone XProtect.

AMAG Symmetry Access is a modular, open-platform access control solution for large enterprises, critical infrastructure, and compliance-sensitive industries. Offered in tier-based editions, it supports up to 512 readers per server, visitor management, advanced analytics, role-based access profiles, and FIPS 201 compliance. With integrations across 100+ technology partners, Symmetry provides a future-proof foundation for unified security in sectors like government, energy, healthcare, and education.

LenelS2 NetBox is a scalable, browser-based access control solution for organizations of any size. From small businesses to global enterprises, it offers advanced features like real-time alarm monitoring, role-based access control, and integration with video surveillance and third-party systems. With flexible deployment options on physical appliances or virtual machines, plus support for Apple Wallet NFC credentials and enhanced Mercury hardware, NetBox provides unified, future-ready security management.

Access control systems rely on more than just software to manage policies and operations. At their core, they depend on robust, enterprise-grade hardware to enforce security protocols and ensure reliable performance at the edge. MCA provides a comprehensive portfolio of access control hardware designed for reliability, security, and seamless integration within on-premises Access Control Management (ACM) environments.
Access control panels and controllers are the brain of any physical access system. Installed on-site, these devices connect directly to door hardware and integrate with ACM software platforms. MCA supports advanced controllers from trusted manufacturers such as Mercury, HID, and Axis, as well as proprietary hardware from brands like Avigilon, LenelS2, Genetec, and AMAG. Key features include encrypted communication, credential caching, and offline functionality, ensuring the system maintains security even if server connections are interrupted.
Readers authenticate user credentials at access points, forming a critical link in any access control system. MCA offers multi-technology readers that support a range of credential types, including proximity cards, smart cards, mobile credentials (via BLE or NFC), biometric identifiers, and PIN codes. Our selection includes OSDP-compliant and FIPS-validated readers for high-security applications. Supported credentials vary from physical ID badges to smartphone-based access tokens, offering flexibility for diverse use cases.
A secure door requires more than just a reader. MCA supplies and supports electronic strikes, magnetic locks, request-to-exit (REX) devices, and fully integrated electrified locksets. These components ensure physical security while enabling remote control through the access control system. We partner with trusted brands like ASSA ABLOY and Allegion, delivering solutions that meet local codes and regulatory compliance.
Reliable power delivery is vital for system uptime. MCA provides UL294-compliant power solutions with integrated battery backups, fire alarm interface modules, and tamper detection features. These power systems are housed in secure, wall-mounted enclosures that align with IT and facility standards. For mission-critical environments, we offer redundant and continuously monitored power systems to maximize reliability.
On-premises ACM platforms require dedicated hardware for optimal performance. MCA provisions fully configured rackmount server appliances, industrial-grade workstations, and mobile-ready terminals—tailored to meet the specific scale and architecture of each deployment. These systems are optimized to securely host ACM software, manage databases, and support video integrations, ensuring seamless operation.
MCA extends the functionality of access control systems with additional hardware such as intercom stations, elevator controllers, intrusion alarm panels, relay I/O boards, and visitor management kiosks. These components integrate ACM functionality with broader building systems, enabling unified management of security, automation, and compliance.
A secure and reliable network is crucial for communication between access control components, management servers, and auxiliary systems. MCA designs and implements industrial-grade network infrastructures, including switches, cabling, patch panels, and Power over Ethernet (PoE) injectors. We tailor network solutions to support Ethernet and fiber connections as needed, implementing VLAN segmentation and Quality of Service (QoS) policies to ensure stability, performance, and security.
Licensing, while not hardware, defines the operational scope of ACM platforms. On-premises systems require proper licensing for controller connectivity, the number of doors, cardholders, and advanced features like video integration or mobile credentials. MCA helps clients navigate initial and ongoing licensing requirements, ensuring their systems are appropriately scaled, budgeted, and ready for future expansion or remote management capabilities. Licensing models differ by manufacturer and can significantly influence functionality and long-term costs.
By providing a complete suite of hardware solutions, MCA ensures your on-premises access control system is built for reliability, security, and future scalability. Whether you're managing a single facility or a vast enterprise, our tailored hardware offerings guarantee seamless integration and long-term performance.
Implementing an on-premises access control management system can raise many questions. Below are answers to some of the most common inquiries to help guide your decision-making process.
An on-premise Access Control Management System (ACMS) is a locally hosted platform designed to manage and enforce access permissions for physical doors, entry points, and restricted areas. All data—such as credentials, event logs, and system configurations—is stored and processed within your organization’s infrastructure, providing complete control, privacy, and ownership.
On-premise systems operate entirely within an organization's internal network, offering greater control, minimal reliance on external providers, and enhanced compliance with regulatory requirements. In contrast, cloud-based solutions are hosted by third-party providers and managed via the internet, offering convenience and remote accessibility but relying on external infrastructure for uptime and updates.
Industries requiring strict compliance, robust data privacy, or operational continuity—such as government, defense, utilities, manufacturing, education, and healthcare—often opt for on-premise solutions. These environments benefit from the data sovereignty, local failover capabilities, and enhanced security that self-managed infrastructure provides.
A comprehensive on-premise ACMS includes access control panels (controllers), door readers, and various credential types such as cards, fobs, and mobile credentials. It also requires servers or appliances to host the ACMS software, along with workstations or browser interfaces for management, and network infrastructure for connectivity. To ensure reliability and security, many deployments additionally include backup power systems and physical enclosures.
Yes, modern on-premise ACMS platforms are highly scalable. They can manage anything from a small number of doors to tens of thousands across multiple campuses. Solutions such as Avigilon Unity Access, LenelS2 OnGuard, and Genetec Synergis are designed for enterprise-wide deployments, offering multi-site synchronization and remote management capabilities.
Absolutely. Many leading ACMS platforms feature open architecture and APIs, enabling seamless integration with video surveillance systems (VMS), alarm panels, visitor management tools, building automation, and identity management systems. MCA specializes in creating unified security ecosystems that streamline operations and improve situational awareness.
On-premise systems empower security-conscious organizations to implement their own network hardening measures, configure custom firewall rules, and, if necessary, operate without internet access. Many platforms also offer advanced cybersecurity features, including end-to-end encryption, zero-trust authentication, certificate management, and role-based access controls.
Yes. While mobile credentials are often associated with cloud-based solutions, many modern on-premise ACMS platforms now support them via secure mobile apps or virtual credential modules. These can be used alongside traditional cards or fobs, providing modern convenience while maintaining localized control.
Licensing models vary by manufacturer and are typically based on factors such as the number of doors, users, and system features (e.g., video integration or biometric authentication). MCA helps clients select the optimal licensing packages to support initial deployment and future scalability, ensuring resources are used efficiently without overpaying or underutilizing.
Yes. MCA offers end-to-end services for on-premise access control systems, including system design, installation, quality assurance, user training, and ongoing technical support. Through our SecurePlan offering, we also provide activity feed monitoring, managed services, and preventive maintenance programs tailored to meet the unique needs and regulatory requirements of each client.
MCA conducts a detailed evaluation of your operational environment, regulatory needs, infrastructure, and long-term security goals to recommend the best Access Control Management System. We analyze factors like facility size, user count, integration needs, scalability, and credential types. Our team provides comparisons, hands-on demos, hardware planning, and licensing guidance to ensure the solution aligns with your current operations and future growth.
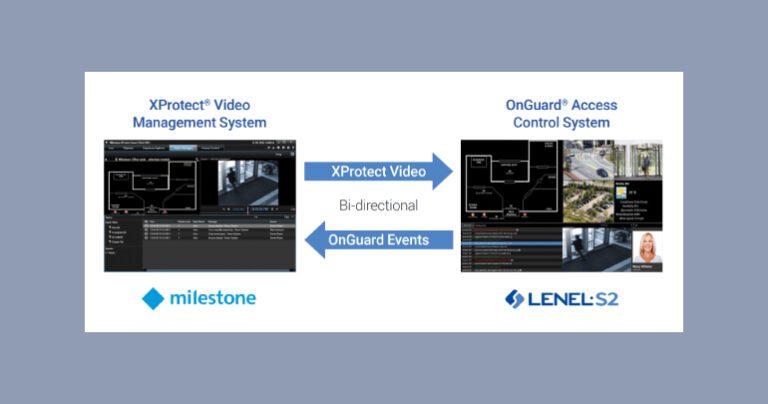
LenelS2 OnGuard and Milestone XProtect integrate seamlessly to unify access control and video surveillance into a scalable ecosystem. This certified solution combines OnGuard’s policy-driven tools with XProtect’s visual insights, enhancing situational awareness and real-time incident response. Operators can stream live or recorded video within the OnGuard interface, linking access events with synchronized footage for faster, smarter decisions. Designed for enterprises, this integration delivers the versatility, scalability, and centralized control needed for efficient access and video security management.
Avigilon Unity, encompassing both its video surveillance and access control components, is an integral part of the overall safety and security ecosystem within Motorola Solutions' "Solving for Safer" Platform. This advanced ecosystem seamlessly integrates video surveillance, access control, radio communications, mass notification systems, and incident management into a single, comprehensive solution. With Avigilon Unity, organizations can enhance safety, security, and efficiency. Paired with MCA’s trusted deployment and support, no other platform offers this level of innovation and integration.

MCA is a trusted leader in providing advanced on-premises access control management solutions. With deep industry expertise, comprehensive support, and a portfolio of top-tier technologies, we work closely with organizations to design and implement tailored ACMS systems. These solutions enhance physical security, streamline administrative processes, and adapt to your operational growth. With MCA, you receive more than a product. You gain a strategic partner dedicated to the reliability, performance, and long-term success of your security infrastructure.
Biometric
Access Controls
Access Control
Management Systems
Access Control
Form Factors
Access Control
System Integrations
Healthcare FacilityAccess Controls
Parking Lot
Access Controls

Security threats are evolving. Is your facility’s protection evolving with them?
From AI-powered surveillance and access control to concealed weapon detection and cloud-based video backup, today’s security landscape demands more than just cameras and locks—it requires integration, automation, and insight.
This quick 20-Point Security Audit helps you evaluate your current systems, uncover hidden vulnerabilities, and identify opportunities for improvement.
Fill out the form below to download the checklist and discover how MCA’s integrated security ecosystems can:
Whether you’re attending GSX or evaluating your next phase of facility protection, MCA is your trusted advisor in next-gen security.