Home » Security Solutions » Access Control Systems » ACMS, ACaaS, & VMS Software » Access-Control-as-a-Service

Modern organizations need security solutions that offer flexibility, rapid deployment, and centralized management across multiple locations. Cloud-Based Access Control Management (ACM) systems (often referred to as Access Control as a Service (ACaaS)), provide a robust alternative to traditional on-premise systems. By utilizing secure cloud infrastructure, these platforms simplify system management, enhance user convenience, and adapt to evolving workplace needs such as hybrid work environments, decentralized teams, and multisite operations.
Unlike traditional systems that require dedicated servers and extensive local IT support, cloud-based ACM solutions allow organizations to manage doors, permissions, credentials, and events remotely from any device, at any time. With features like native mobile credentialing, automatic software updates, and built-in redundancy, these systems reduce operational complexity while improving both security and scalability. MCA’s cloud-ready access control solutions deliver the agility and automation that enterprises need to meet today’s security challenges.
Cloud-Based Access Control Management platforms are hosted in highly secure, redundant cloud environments, eliminating the need for on-premise servers or traditional IT infrastructure. These systems deliver real-time decision-making, remote management, and automated software updates via intuitive browser or mobile interfaces.
With cloud ACM platforms, security teams can seamlessly monitor and control access across multiple facilities, assign digital credentials, configure user roles, and generate actionable reports—all from any internet-enabled location. Featuring role-based administration, elastic scalability, and seamless integration with cloud-native systems like video management and identity platforms, these solutions offer a modern, forward-thinking approach to security.
For organizations focused on efficiency, user experience, and streamlined deployment, Cloud ACMS and ACaaS solutions provide secure, cost-effective, and adaptable pathways to enterprise-grade access control, eliminating the complexities of traditional infrastructure.

Avigilon Alta Access is a fully cloud-native Access Control Management System (ACMS) designed for organizations that need secure, scalable, and intelligent access control without the hassle of maintaining on-site servers or complex infrastructure. With its flexible design and remote visibility, Alta Access allows security teams to efficiently manage doors, users, and events in real-time from anywhere.
Built entirely in the cloud, Alta Access eliminates the need for local controllers or dedicated servers, offering organizations unparalleled convenience and scalability. Security teams can manage access remotely across a single site or multiple locations while receiving real-time alerts on unauthorized access or system anomalies. Automated firmware and security patch updates ensure the system is always current and compliant, while the cloud infrastructure seamlessly scales to support growing operations without the need for additional hardware.
Alta Access delivers a modern, frictionless experience for users and guests through mobile credentials and touchless access capabilities. With features like Wave to Unlock, Apple Watch integration, and mobile apps, users can unlock doors effortlessly. Digital guest passes with time-based permissions simplify visitor access and reduce the need for managing physical credentials. The platform also supports multi-factor authentication, including PINs, biometrics, and device-based verification, adding an extra layer of security.
Alta Access leverages advanced AI to improve automation and provide actionable insights, streamlining daily operations and enhancing situational awareness. Security teams can customize workflows for access events, alarms, or lockdown scenarios while monitoring occupancy and usage trends to maintain compliance. The system generates detailed reports that highlight access anomalies and usage patterns, offering a clear view of facility security. Seamless integration with Alta Video adds another level of security by pairing access logs with video verification.
Security lies at the core of Alta Access, with end-to-end encryption protecting all credential and log data. The platform's tamper-resistant hardware is designed with embedded protections to meet stringent industry standards, including UL, CE, RoHS, and FCC requirements. Automatic firmware updates ensure the system is always protected against emerging threats, making it a reliable solution for regulated industries.
Alta Access is designed for quick installation and deployment, with plug-and-play hardware that simplifies setup and accelerates time-to-value. Its cloud-native controllers, readers, and wireless locks support Power over Ethernet (PoE), reducing cabling costs and making deployment more efficient. Organizations can easily expand to new locations without adding additional head-end infrastructure, and remote provisioning tools make setting up new doors a matter of minutes.
Alta Access supports robust integrations with a variety of systems, enabling organizations to create a unified and efficient security ecosystem. It connects seamlessly with platforms like Microsoft Azure, Google Workspace, and Active Directory, while also integrating with alarms, environmental sensors, and AI-powered video systems. This level of adaptability allows workflows for emergency events and facility control to be automated, enhancing overall operational efficiency.
Alta Access is well-suited for a wide range of industries, making it a versatile tool for distributed and modern work environments. It supports multi-site corporate offices, campuses, healthcare facilities, educational institutions, retail and hospitality operations, logistics hubs, and mixed-use commercial or industrial spaces. By combining cloud-native flexibility with advanced security features, Alta Access delivers a comprehensive access control solution that meets the demands of today’s dynamic workplaces.

MCA provides a carefully selected portfolio of cloud-native and hybrid access control platforms designed to address diverse operational, compliance, and IT needs. These Access Control as a Service (ACaaS) solutions offer flexible deployment options, centralized management, and robust cybersecurity. Ideal for modern enterprises, they deliver scalability, automation, and real-time visibility across multiple locations. Below are a few featured offerings from our trusted technology partners.

Genetec’s Security Center SaaS (SC SaaS) platform offers advanced cloud-native security with Access Control as a Service (ACaaS) at its core. It delivers centralized identity management, real-time access control, and scalable credentialing via a web-based interface. Integrating seamlessly with VSaaS and cloud-managed devices, it enhances compliance, reduces IT overhead, and streamlines operations. Leveraging Synergis Cloud Link for hybrid deployments, SC SaaS supports AI-driven forensic search and predictive OPEX pricing, providing a flexible, scalable solution.

LenelS2 Elements is built for today’s mobile-first, cloud-first organizations, offering unified access control and video surveillance through a fully cloud-native interface. Hosted on Microsoft Azure, it features role-based credentialing, integrated video verification, and real-time lockdown capabilities. Accessible via web browser or mobile device, it simplifies IT management while delivering powerful security insights. LenelS2 Elements is ideal for small to mid-sized businesses and multi-site enterprises seeking a scalable, user-friendly solution.

OnGuard Cloud enhances LenelS2’s OnGuard platform by delivering enterprise-grade features like visitor management, lockdown automation, and multi-factor authentication in a secure AWS-hosted cloud environment. Compliant with FIPS and FedRAMP standards, it eliminates the need for local server maintenance, enabling a smooth transition to the cloud without sacrificing functionality or third-party integrations. Ideal for organizations seeking robust ACaaS solutions with enterprise-level performance.

Feenics is a cloud-native ACaaS platform designed for automation, cybersecurity, and mobile accessibility. Hosted on AWS, it features real-time credentialing, remote lockdowns, and system-wide visibility through an intuitive web or mobile interface. Feenics integrates easily with video, intrusion, visitor management, and smart lock systems, enabling businesses to scale security operations while minimizing their IT footprint. Its open integration framework and robust architecture make it an excellent choice for enterprise, healthcare, and education applications.

Genea Cloud is a modern access control platform designed for flexibility, scalability, and real-time management. Compatible with non-proprietary Mercury and HID hardware, it offers features like remote credentialing, mobile key issuance, global activity monitoring, and instant lockdowns, all managed through a unified cloud-based dashboard. Integrating with leading systems such as Avigilon Unity and Alta for video-verified access, and automation tools like Okta and Slack, Genea simplifies security management for enterprises.

DMP’s Remote Link software provides cloud-based panel management for integrators and organizations using DMP’s XR and XT Series control panels. While not actually an ACaaS platform, it enables remote programming, diagnostics, credential management, and firmware updates across multiple sites from a single workstation via the cloud. This solution is particularly suited for private security firms and commercial integrators looking to streamline service and support without physical site visits. It’s a practical tool for efficient, remote security system management.

Our cloud-based systems are built on a combination of key components that work together to deliver secure, flexible, and scalable access management. From authentication methods and authorization protocols to centralized management tools and physical hardware, each element plays a critical role. Below we explore the essential components of an ACaaS solution, breaking down how they function and integrate to secure modern environments.
Authentication serves as the first line of defense, ensuring user identities are verified before access is granted. Advanced Access Control as a Service (ACaaS) systems support a variety of credential types, including mobile credentials, biometrics such as facial or fingerprint recognition, and traditional physical tokens like key cards and fobs. Many platforms also incorporate multi-factor authentication (MFA), combining two or more verification methods to enhance security. Mobile-based credentials are especially popular due to their convenience and reduced administrative overhead, allowing users to access facilities through secure smartphone applications.
Once a user’s identity is authenticated, authorization determines which doors they can access and during what time periods. Role-based access control (RBAC) allows administrators to configure detailed access rules tailored to specific user groups, departments, or individual needs. These permissions can be instantly modified and enforced across multiple locations in real time. ACaaS platforms also support advanced features like time-based access schedules, visitor permissions, and emergency lockdown protocols, all of which can be centrally managed for seamless policy enforcement.
The management layer of a cloud-based access control system offers a unified dashboard for overseeing the entire access ecosystem. Accessible via web browsers or mobile apps, this interface allows administrators to monitor live access events, update user credentials, configure hardware settings, and respond to alarms in real time. Reporting and analytics tools are also built into the platform, enabling compliance audits and in-depth activity tracking. By eliminating the need for local servers, IT teams are freed from routine maintenance tasks such as software updates, patches, and hardware repairs.
While cloud-based systems rely on centralized infrastructure, they still require on-site hardware to secure physical entry points. Credential readers communicate with cloud controllers to validate access requests, while electrified locks and wireless locksets secure doors until proper authorization is confirmed. Additional devices, such as door position sensors and request-to-exit devices, enhance security visibility by tracking door status and ensuring safe egress. Many of these components are network-connected and PoE-enabled, simplifying installation and reducing infrastructure costs.
The intelligence and data behind cloud-based access control systems are hosted in secure cloud environments maintained by the service provider. This includes the application layer, access permissions database, and event logs. Cloud hosting eliminates the need for server rooms, reducing overall costs and simplifying infrastructure. Providers also ensure robust cybersecurity, system redundancy, and high availability, enabling administrators to access the system anytime, anywhere, with an internet connection.
To optimize security and operational efficiency, cloud-based access control systems integrate seamlessly with third-party platforms. For example, video surveillance systems can pair access events with real-time footage, while alarm systems can trigger responses to unauthorized access or forced entry attempts. Visitor management systems can issue temporary credentials and log access histories for non-employees. These integrations create a unified security environment, supporting both immediate responses and detailed forensic investigations.
By combining advanced technology, centralized control, and seamless integrations, cloud-based access control systems offer a robust, scalable solution for securing today’s fast-evolving environments.
Implementing a cloud-based access control management system can raise many questions. Below are answers to some of the most common inquiries to help guide your decision-making process.
ACaaS refers to cloud-based access control management systems that offer centralized credentialing, real-time monitoring, and access policy enforcement without requiring on-site servers. These platforms are hosted in secure cloud environments and can be accessed remotely via web or mobile interfaces.
Unlike traditional on-premise systems, ACaaS solutions do not require local server infrastructure. This reduces IT overhead and simplifies deployments across multiple locations. ACaaS platforms provide faster updates, greater scalability, and easier remote management, making them ideal for organizations with evolving security needs or limited IT resources.
ACaaS is particularly beneficial for distributed enterprises such as retail chains, property management firms, healthcare networks, educational institutions, and commercial office buildings. It is especially effective for environments that need centralized control across numerous locations or temporary access provisioning for contractors and visitors.
Yes. Leading ACaaS platforms deliver enterprise-grade security features, including end-to-end encryption, multi-factor authentication, role-based access, and zero-trust frameworks. Many solutions are hosted on highly secure platforms like Microsoft Azure or AWS and comply with industry standards such as SOC 2, GDPR, and FedRAMP.
Yes, most modern ACaaS platforms are built with open APIs that support seamless integration with systems like VSaaS (Video Surveillance as a Service), intrusion detection, visitor management, and identity verification. This unified approach enhances situational awareness and automates response workflows.
ACaaS platforms maintain local controller-based intelligence at the edge, allowing doors to operate based on stored rules and credentials even if internet connectivity is interrupted. Once connectivity is restored, all activity is synchronized with the cloud. Some solutions also support offline fallback modes and redundant network pathways.
ACaaS is designed to scale effectively. Organizations can manage anywhere from a few doors to thousands across multiple buildings, campuses, or geographic locations, all through a single cloud-based dashboard. Expanding the system is as simple as adding licenses, with no need for additional hardware or infrastructure upgrades.
Yes. MCA works closely with clients to assess facility needs, compliance requirements, and existing infrastructure. Our team helps identify the most suitable ACaaS platform from our portfolio of trusted manufacturers, oversees installation and integration, and provides training, documentation, and ongoing support throughout the system's lifecycle.

Avigilon Alta Access integrates with Milestone XProtect to unify cloud-based access control with real-time video surveillance, enhancing situational awareness and proactive threat management. This certified integration links access events with video footage, enables door lock control within XProtect, and provides instant alerts for critical incidents like forced entries or doors left open. Designed for enterprises, it streamlines security workflows by combining visual insights with access activity, allowing teams to quickly detect anomalies, investigate incidents, and ensure compliance across complex facilities.
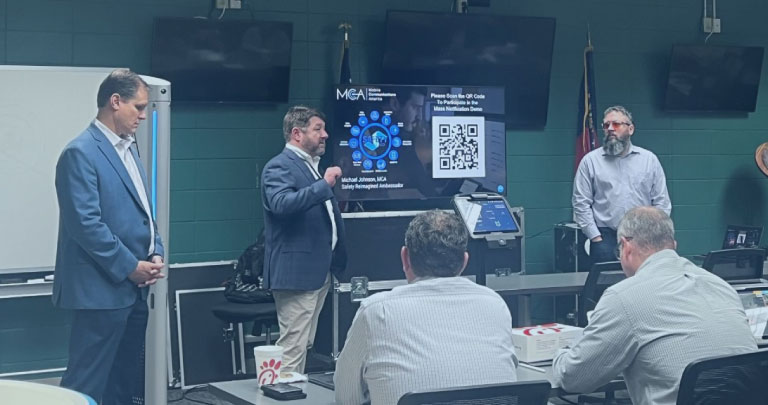
Avigilon Alta, Motorola Solutions’ cloud-native access control and video management platform, plays a critical role in the broader “Solving for Safer” ecosystem. As part of this fully integrated solution, Alta enables real-time access control, AI-powered video surveillance, and seamless collaboration with radio systems, mass notification tools, and incident management platforms, all from a unified, cloud-based interface. With Alta, organizations gain unmatched flexibility, scalability, and situational awareness. With MCA’s expert support, the Avigilon Alta platform delivers intelligent, future-ready security.

MCA is a trusted provider of secure, cloud-based access control solutions that help organizations modernize their physical security with flexibility, scalability, and efficiency. Our team collaborates closely with clients to design and implement customized ACaaS platforms that centralize control, minimize IT workload, and seamlessly support multi-site operations. Powered by advanced technologies and expert support, MCA delivers more than just a service. We are a long-term partner dedicated to the success, adaptability, and resilience of your access control strategy.
Biometric
Access Controls
Access Control
Management Systems
Access Control
Form Factors
Access Control
System Integrations
Healthcare FacilityAccess Controls
Parking Lot
Access Controls

Security threats are evolving. Is your facility’s protection evolving with them?
From AI-powered surveillance and access control to concealed weapon detection and cloud-based video backup, today’s security landscape demands more than just cameras and locks—it requires integration, automation, and insight.
This quick 20-Point Security Audit helps you evaluate your current systems, uncover hidden vulnerabilities, and identify opportunities for improvement.
Fill out the form below to download the checklist and discover how MCA’s integrated security ecosystems can:
Whether you’re attending GSX or evaluating your next phase of facility protection, MCA is your trusted advisor in next-gen security.