Understanding the New Challenges Facing Telecom Security
In an era where cyber threats are evolving at an unprecedented pace, Nokia’s latest press release and web content shed light on the alarming rise of Distributed Denial of Service (DDoS) attacks and the innovative solutions the company is deploying to address these challenges. Drawing from their 11th annual Threat Intelligence Report and cutting-edge technologies, Nokia emphasizes the need for AI-driven, adaptive security measures to protect critical networks from increasingly sophisticated cyberattacks.
DDoS (Distributed Denial of Service): A cyberattack that floods a network or service with excessive traffic, disrupting normal operations.
AI-Driven Defense: A cybersecurity approach that uses artificial intelligence and machine learning to detect, predict, and neutralize threats automatically.
The Growing Threat Landscape
Nokia’s Threat Intelligence Report highlights a surge in stealthy intrusions and record-breaking DDoS attacks targeting telecom operators and critical infrastructure. Key findings include:
Stealthy Intrusions: Nearly 63% of telecom operators experienced at least one “living off the land” attack in the past year, with 32% facing four or more. These attacks exploit trusted tools, unpatched devices, and misconfigurations to infiltrate core networks, often leading to long-term data exposure and costly remediation.
DDoS Escalation: Terabit-scale DDoS attacks have become a daily occurrence, with peaks reaching 5 to 10 Tbps. These attacks are shorter but more powerful, with 78% ending within five minutes and 37% concluding in under two minutes. Over 100 million residential endpoints are now compromised, amplifying the threat.
AI and Quantum-Safe Networking: Over 70% of telecom security leaders prioritize AI- and ML-based threat analytics, with more than half planning to deploy AI for detection within 18 months. Additionally, the industry is beginning to address the need for quantum-safe encryption to prepare for future cryptographic challenges.
Quantum-Safe Encryption: Cryptographic methods designed to withstand decryption by future quantum computers.
Understanding DDoS Attacks
DDoS attacks aim to overwhelm networks, denying access or degrading connectivity for users and infrastructure. These attacks manifest in three primary forms:
- Amplification and Reflection DDoS: Exploiting system vulnerabilities to amplify attack traffic.
- Flooding DDoS: Using IP address spoofing or header modification to overwhelm targets.
- Application-Layer DDoS: Targeting specific applications or services to disrupt functionality.
The rise of insecure IoT devices and residential proxies has fueled the growth of hyper-volumetric, multi-terabit DDoS attacks. These attacks are increasingly automated and AI-driven, enabling attackers to adapt tactics in real-time, making detection and mitigation more challenging.
The Impact on Service Providers
DDoS attacks have far-reaching consequences for service providers, cloud builders, and enterprises:
- Degraded Services: Residential and enterprise customers experience reduced quality of service, impacting activities like gaming, streaming, and business operations.
- Financial and Reputational Damage: High-bandwidth attacks can result in significant financial losses, legal liabilities, and reputational harm.
- Regulatory Compliance: Stricter security regulations, such as the EU’s NIS2 directive, require providers to minimize the impact of attacks and report incidents promptly.
Nokia’s Next-Generation DDoS Security Solutions
To address these challenges, Nokia has developed a comprehensive, AI-driven DDoS security solution that integrates advanced analytics, network programmability, and automated mitigation. Key components include:
Deepfield Defender
Deepfield Defender is Nokia’s flagship software application for DDoS detection and mitigation. It combines network telemetry with Nokia’s patented Deepfield Secure Genome®, a cloud-based data feed that tracks the security context of the internet. Key features include:
- Real-Time Detection: AI-driven algorithms analyze network traffic in real-time, identifying anomalies with high accuracy.
- Automated Mitigation: The system deploys optimized, automated responses tailored to specific attack vectors, minimizing collateral damage.
- Continuous Learning: A closed-loop system continuously refines AI models based on real-world attack data, improving detection and mitigation over time.
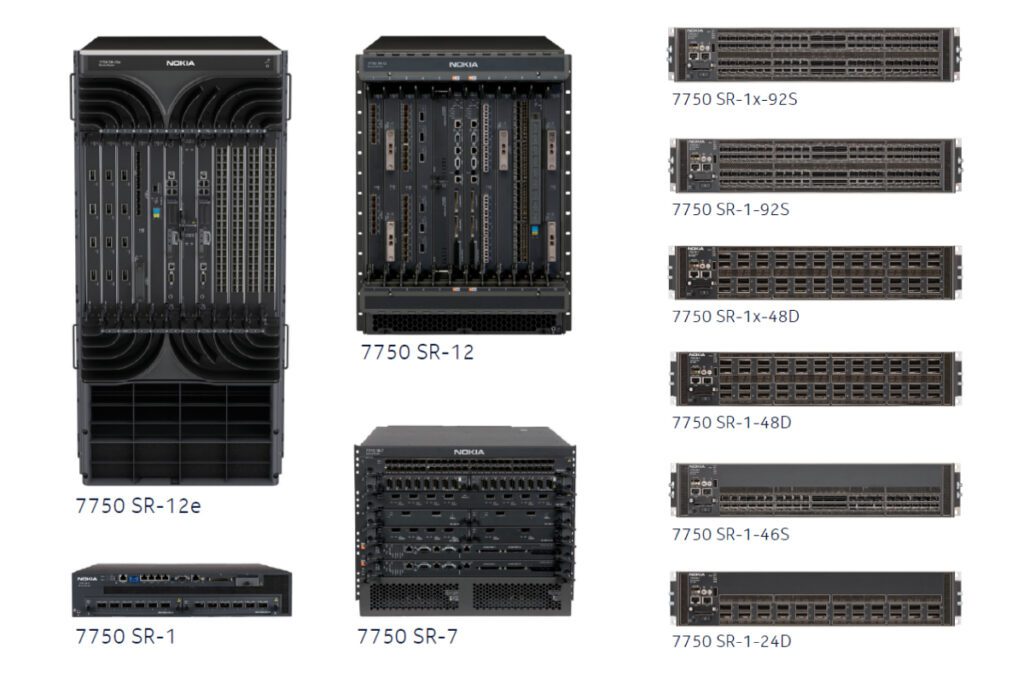
7750 Defender Mitigation System
The 7750 Defender Mitigation System (DMS) is a next-generation platform designed for terabit-scale DDoS mitigation. Powered by Nokia’s FP5 network processor technology, the 7750 DMS offers:
- High Performance: With 2.8 Tbps of mitigation capacity, the system can handle even the largest attacks.
- Advanced Countermeasures: The system’s Advanced Countermeasures Engine (ACE) enables stateful inspection of IP packets, combating volumetric, botnet, and application-layer attacks.
- Flexible Deployment: The compact design allows for centralized or distributed deployment, providing comprehensive protection across all network entry points.
FP5 Network Processor: Nokia’s proprietary chip architecture providing high-speed data processing and DDoS mitigation at terabit scale.
AI-Driven Defense Architecture
Nokia’s approach leverages the network itself as a sensor and enforcer, transforming routers into active mitigation platforms. By integrating AI-driven intelligence with programmable network hardware, Nokia enables:
- Scalable Defense: Modern routers enforce granular filtering rules at line rate, stopping malicious traffic closer to its source.
- Cost Efficiency: Service providers can leverage existing network infrastructure, reducing the need for additional security appliances.
Managed Security Services and Beyond
Nokia’s Deepfield Defender also supports Managed Security Service Provider (MSSP) functionality, enabling service providers to offer premium DDoS protection services to their customers. This creates new revenue streams while enhancing network security.
Nokia’s comprehensive DDoS security solution represents a paradigm shift in network defense. By combining AI-driven analytics, advanced mitigation platforms, and network programmability, Nokia empowers service providers to stay ahead of evolving threats. As cyberattacks grow in scale and sophistication, Nokia’s innovative approach ensures that critical networks remain secure, resilient, and ready for the challenges of tomorrow.
Deepfield Secure Genome®: Nokia’s continuously updated cloud-based database that provides real-time visibility into malicious internet activity.
MSSP (Managed Security Service Provider): A company that delivers outsourced monitoring and management of security systems and devices.
Partnering with MCA for Scalable Network Protection
At MCA, our Network Infrastructure Solutions team is committed to helping utilities, railways, telecoms, and other enterprises with expansive and complex networks achieve robust, future-ready security. As Nokia’s top partner in the United States, we leverage industry-leading technologies to support critical infrastructure and ensure operational continuity.
Our approach begins with a comprehensive evaluation of your unique network environment. Working closely with your teams, we assess your current challenges and objectives to recommend the right combination of Nokia solutions and other technology platforms as needed. MCA’s collaborative methodology ensures that every design prioritizes performance, resilience, and ease of management – built precisely to your requirements.
With our experienced team members guiding every phase – from initial consultation and solution design to deployment and lifecycle support – you benefit from a solution tailored for your scale, growth, and security priorities. MCA is proud to be the trusted partner for organizations seeking integrated, scalable protections for their most vital assets.
To explore how Nokia’s DDoS security solutions, delivered in partnership with MCA, can safeguard your networks, contact our Network Infrastructure Solutions team to begin a detailed assessment and technology review. MCA’s extensive portfolio ensures that we recommend the optimal mix of solutions – whether from Nokia or another leading provider – to meet your operational needs now and in the future.
MCA serves enterprise and public-sector organizations across the United States through more than 100 regional Solution Centers, offering local consultation, implementation, and lifecycle support for Nokia’s advanced network security solutions.
Frequently Asked Questions
A Distributed Denial of Service (DDoS) attack overwhelms a targeted network or service with massive traffic from multiple sources, causing service disruption or downtime.
Effective DDoS protection combines AI-powered analytics, automated threat detection, layered network monitoring, and responsive mitigation tools like Nokia’s Deepfield Defender and 7750 DMS.
Modern defenses emphasize real-time AI detection, network programmability, and using routers as active mitigation nodes. Service providers increasingly adopt quantum-safe encryption and Managed Security Services for long-term resilience.
Deepfield Defender uses AI algorithms with the Deepfield Secure Genome® to analyze global threat data and automate real-time countermeasures tailored to each attack vector.
MCA works directly with telecom and enterprise clients to assess vulnerabilities, design scalable protection strategies, and deploy Nokia’s integrated DDoS solutions for long-term network resilience.
About MCA
We believe every workplace should be safe, secure, and efficient. As trusted advisors, we deliver integrated communication, connectivity, and security solutions with a Service First mindset – driven by a team that cares deeply about our customers and each other.
Why MCA? At MCA, we help solve critical communication, connectivity, and security challenges with turnkey, integrated system solutions – from two-way radios and in-building wireless to video surveillance, access control, and more. MCA is built from over 50 companies with deep technical expertise and strong local roots. And we’re still growing – expanding our capabilities, our reach, and our team.
Our 100+ Solution Centers bring together sales, installation, service, and customer operations teams to deliver seamless, nationwide support. Guided by our Service First value, we don’t just connect the wires and walk away – we provide customized solutions backed by deep expertise and lifecycle support.


