Orchestrate: Automating Security and Operations for Maximum Efficiency
Introduction to Orchestrate
In today’s fast-paced and security-driven environments, organizations must be proactive, efficient, and highly responsive to potential threats, operational inefficiencies, and service disruptions. Orchestrate, Motorola Solutions’ cloud-based automation platform, brings intelligence and control to security workflows by integrating video surveillance, access control, radio communications, and software analytics into a single, cohesive system.
By leveraging AI-powered automation and decision-based logic, Orchestrate empowers businesses to respond more effectively to security threats, optimize their operational processes, and improve workforce efficiency. From corporate campuses to retail, healthcare, and critical infrastructure, Orchestrate ensures a proactive security approach that maximizes response time while reducing manual effort.
What is Orchestrate?
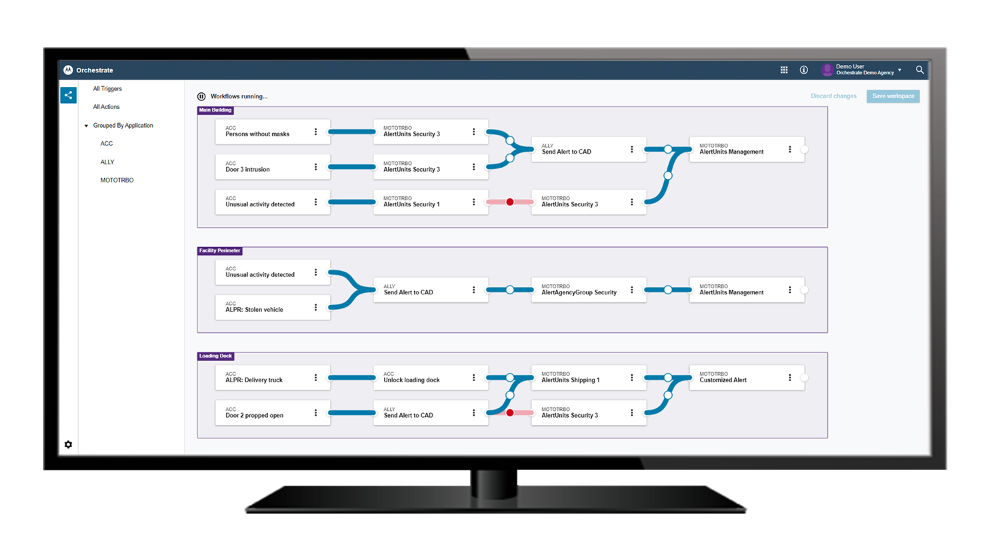
Orchestrate is an intelligent security and operations automation platform that allows businesses to configure rule-based workflows that integrate across Motorola Solutions’ ecosystem, including video surveillance, access control, radio communications, and digital alerts.
Rather than relying on manual responses to incidents, Orchestrate enables businesses to automate workflows, ensuring security teams and employees receive real-time notifications when critical events occur. By automatically triggering alerts, activating security protocols, and escalating responses, Orchestrate allows organizations to focus on what matters most—protecting people, assets, and operations.
Key Features of Orchestrate
1. Intelligent Automation and Workflow Creation
- Orchestrate enables users to build custom automated workflows using an intuitive drag-and-drop interface.
- Users can connect and automate workflows across multiple security and operations systems, improving decision-making and response time.
- Automate incident response procedures, facility lockdowns, and access control actions based on pre-set conditions.
2. Centralized, Cloud-Based Platform
- Orchestrate is hosted in the cloud, offering anywhere, anytime access to security workflows and incident automation.
- Eliminates the need for on-premise servers, reducing IT burden and enhancing security reliability.
- Seamless software updates ensure organizations always benefit from the latest features without downtime.
3. Real-Time Event and Threat Monitoring
- Leverages AI-driven analytics and connected security devices to monitor real-time threats.
- Automatically detects anomalies using integrated video analytics, sensors, and access control events.
- Configurable rules engine triggers security workflows based on predefined parameters.
4. Seamless Integration Across the Motorola Solutions Ecosystem
Orchestrate connects and automates workflows across a wide range of Motorola Solutions’ security and operations products, including:
- Avigilon Unity & Alta (video surveillance, access control, AI-powered analytics)
- MOTOTRBO™ Two-Way Radios (instant voice communication and automated alerts)
- WAVE PTX™ (push-to-talk broadband communications)
- Ally™ Incident Management (incident tracking, workflow management, and response coordination)
- Aware Enterprise (real-time personnel tracking and resource mapping)
- Rave Alert & Panic Button (emergency mass notification and critical response)
5. Automated Alerts and Notifications
- Real-time notifications can be sent via radio alerts, SMS, emails, or push-to-talk messages.
- Triggers automated alerts for security breaches, unauthorized access, or emergencies.
- Customizable event prioritization ensures the most critical incidents receive immediate attention.
6. Data-Driven Insights for Better Decision-Making
- Collects and analyzes security data to optimize response workflows.
- AI-powered analytics identify security patterns and trends, improving operational efficiency.
- Integrates license plate recognition, facial recognition, and alarm triggers into response protocols.
Key Benefits of Orchestrate
1. Faster, More Effective Incident Response
- Orchestrate reduces manual delays in incident management by automating response workflows.
- Security teams receive immediate alerts and can act faster to prevent escalation.
2. Increased Operational Efficiency
- Businesses can reduce labor-intensive security tasks by automating routine processes.
- Workflows eliminate inefficiencies and ensure consistent execution of security protocols.
- Less time spent on manual monitoring means more focus on strategic initiatives.
3. Improved Situational Awareness
- A centralized, real-time view of operations provides greater visibility into security incidents.
- AI-powered analytics filter out false alarms and prioritize critical threats, ensuring resources are deployed efficiently.
4. Seamless Integration and Scalability
- Works with existing infrastructure while offering flexibility for future technology expansion.
- Easily integrates with existing security ecosystems to scale with organizational growth.
- Supports multi-site operations, making it ideal for enterprises with dispersed locations.
5. Cost Reduction and ROI Optimization
- Reduces the cost of manual monitoring, false alarms, and security breaches.
- Lowers operational costs by minimizing human intervention in repetitive security tasks.
- Protects employees, customers, and assets, mitigating financial losses from security incidents.

Applications of Orchestrate in Different Industries
Orchestrate enhances security and operational efficiency across a wide range of industries, ensuring seamless automation of responses, real-time alerts, and improved situational awareness.
Corporate Offices & Industrial Sites
In corporate offices, industrial sites, and manufacturing plants, Orchestrate automates access control and video surveillance monitoring, ensuring that only authorized personnel enter restricted areas. The system can trigger immediate alerts for perimeter breaches or unauthorized loitering, safeguarding both employees and critical infrastructure.
Retail & Hospitality Environments
For retail environments, hotels, and resorts, Orchestrate strengthens security by automatically locking doors in response to emergency situations. AI-powered analytics identify suspicious behavior, such as theft patterns, and notify security teams in real time, allowing for a rapid response that enhances guest and customer safety.
Hospitals and Medical Centers
In healthcare facilities and medical centers, Orchestrate integrates seamlessly with panic buttons and emergency alert systems to protect patients and staff. Video analytics continuously monitor restricted areas to prevent unauthorized access to sensitive medical zones, pharmaceuticals, and high-risk patient areas.
Institutions of Higher Education
On large college campuses and educational institutions, Orchestrate provides automated lockdown procedures and rapid response capabilities during security threats. AI-driven analytics detect and escalate alerts for suspicious behavior, ensuring the safety of students, faculty, and visitors.
Public Venues
Airports, stadiums, and arenas benefit from Orchestrate’s ability to manage security across vast spaces with high foot traffic. Automated workflows integrate with video surveillance and access control to monitor crowd movement, detect suspicious activity, and deploy security personnel where they are needed most.
Public Safety Agencies
For public safety agencies, Orchestrate acts as a force multiplier, automating critical workflows such as real-time dispatch alerts, geofencing unauthorized areas, and integrating video surveillance feeds with emergency response systems. This enhances situational awareness for law enforcement, fire departments, and emergency medical services.
Transportation & Logistics
In transportation and logistics hubs, including shipping yards and warehouse facilities, Orchestrate improves fleet and cargo security by automating license plate recognition for unauthorized vehicle entry. The system integrates with dispatch and radio communications to streamline fleet tracking and real-time incident reporting.
Across all these industries, Orchestrate optimizes security, improves response times, and ensures a seamless integration of security technologies, making operations more efficient and proactive.
Why Choose Orchestrate for Your Business?
Orchestrate is more than just an automation tool—it is a comprehensive security and operations management platform that enhances situational awareness, improves incident response, and reduces operational inefficiencies. Its ability to integrate with Motorola Solutions’ security ecosystem makes it the ideal choice for businesses looking to streamline security, automate workflows, and maximize operational efficiency.
With real-time alerts, AI-powered decision-making, and cloud-based management, Orchestrate ensures that businesses remain resilient, secure, and prepared for any situation.
Why Choose MCA for Orchestrate?
As a leading provider of security and communications solutions, MCA offers unmatched expertise in deploying Orchestrate for various industries. We customize solutions to fit your organization’s needs, ensuring seamless integration, training, and ongoing support.
By partnering with MCA, your business gains access to cutting-edge security technology, customized automation solutions, and industry-leading customer support—all designed to help you achieve smarter, safer, and more efficient operations.
Orchestrate is a game-changer for security and operations automation. Take control of your security ecosystem today—automate your workflows, streamline responses, and optimize efficiency with Orchestrate from MCA.


