Detect And Intercept Drones To Maintain Critical Security
Counter-drone technology, also known as counter-unmanned aerial vehicles (UAV), encompasses a range of systems designed to detect and intercept drones. This technology has evolved in response to the increasing adoption of drones in both civilian and military settings. The rise of counter-UAV solutions is directly linked to growing concerns about the potential threats drones pose in various environments.
In various sectors, deploying C-UAV technology is critical to maintaining security and safeguarding assets against unauthorized drone activity.
Critical Infrastructure Protection
Critical infrastructure, such as power plants, water treatment facilities, and transportation hubs, is a prime target for malicious drone activity. Rogue drones could conduct surveillance, disrupt operations, or even carry out physical attacks. Implementing C-UAV measures is essential to detect and neutralize such threats, ensuring critical infrastructure assets’ continuous operation and resilience.
Law Enforcement
Law enforcement agencies and public safety organizations rely on maintaining order and protecting citizens from various threats. Drones can be utilized for illicit activities such as smuggling contraband, conducting surveillance on law enforcement operations, or interfering with emergency response efforts. Integrating C-UAV technology into security plans enables proactive detection and interdiction of unauthorized drones, enhancing public safety and supporting law enforcement objectives.
Event Security
Events with large crowds, such as concerts, festivals, and sporting events, are susceptible to security risks posed by drones. Unauthorized drones flying over crowded venues can pose significant safety hazards, including the risk of collisions or potential terrorist attacks. Deploying C-UAV systems allows event organizers to establish no-fly zones, detect unauthorized drone activity, and implement appropriate mitigation measures to ensure the safety and security of attendees.
Military and Defense
Protecting military installations, forward operating bases, and deployed personnel from enemy drones is paramount in military and defense applications. Hostile UAVs could be used for reconnaissance, surveillance, or even weapon delivery, posing serious threats to operational security and personnel safety. Integrating C-UAV technologies into military security plans enables early detection and interception of hostile drones, preserving mission integrity and reducing vulnerabilities to adversarial UAV threats.
Prison Security
Prisons and correctional facilities face unique challenges in preventing unauthorized items from being delivered to inmates via drones. Smuggling contraband, such as drugs or weapons, using drones poses a significant security risk and compromises the safety of staff and inmates. Implementing C-UAV measures, such as drone detection systems and mitigation technologies, helps prison authorities detect and disrupt illicit drone activity, enhancing facility security and preventing contraband smuggling.
Border Security
Border control agencies tasked with monitoring and securing national borders face increasing challenges from drones used for smuggling, illegal surveillance, or incursions into restricted airspace. Unauthorized drones can evade traditional border security measures, posing national security and sovereignty threats. Deploying C-UAV systems along border regions enables timely detection and interception of rogue drones, enhancing border surveillance capabilities and preventing illicit activities.

Types of C-UAV Technologies
Counter-UAV measures can be broadly categorized into two main types: drone detection and drone mitigation or interception.
Drone Detection
Drone detection technology is designed to identify drones operating within a designated airspace. Detection methods include radar, RF sensors, and PTZ cameras. These systems can locate drones and provide critical information such as the drone’s flight path, pilot location, and telemetry data.
Drone Mitigation
Drone mitigation or interception technology involves electronically or physically disrupting drone operations. Mitigation methods include:
Jammers: Disrupt the communication link between the drone and its operator.
Spoofers: Deceive the drone’s GPS or communication system to take control of it.
Nets: Physically capture the drone.
Security Drones: Drones designed to intercept or neutralize rogue drones.
While the terminology around these methods can be used interchangeably, there is a distinct difference between detection and mitigation. Detection is about awareness, while mitigation involves active measures to neutralize threats.
Legal Considerations for Counter-Drone Measures
While various counter-drone measures are available, not all are legal in many countries. In the United States, signal jammers are restricted to federal agencies such as the Departments of Defense, Homeland Security, and Justice. However, drone detection methods using RF and radar are legal and widely implemented to enhance airspace security.
MCA’s Partner Solutions Strengthen Security
AirSight
AirSight’s AirGuard solution offers a comprehensive and cutting-edge approach to counter-drone technology. It provides advanced drone detection capabilities to enhance airspace security. Leveraging state-of-the-art radar, RF sensors, and PTZ cameras, AirGuard effectively detects unauthorized drone activity, providing real-time situational awareness to security personnel.
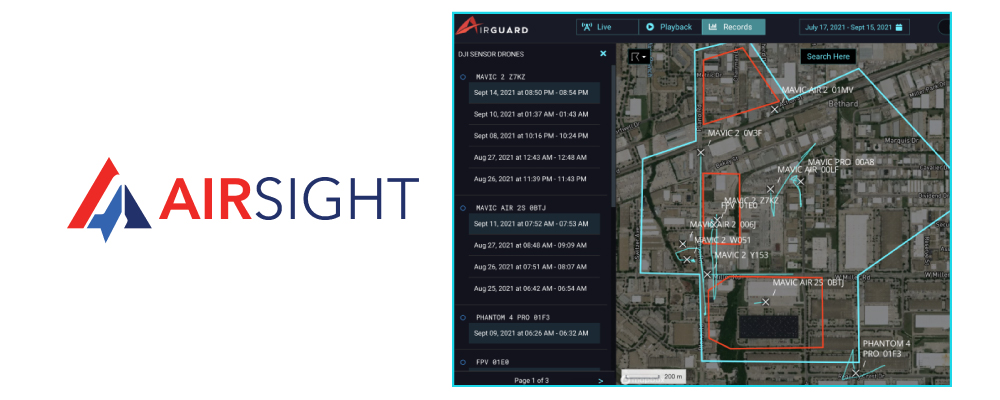
AirGuard can also identify intruding drones and pinpoint the pilot’s location, flight path, and other critical telemetry data, empowering security teams to take informed and decisive actions. With its user-friendly interface and robust features, AirGuard is a trusted solution for safeguarding critical infrastructure, public safety, military installations, and other high-risk environments against the growing threat of rogue drones.
Silent Sentinel
Silent Sentinel is a leading provider of electro-optical (EO) platforms in the counter-unmanned aerial systems (C-UAS) market. Utilizing the modular Jaegar platform, Silent Sentinel offers a comprehensive range of C-UAS technologies, including thermal and video target acquisition, video tracking, and various mitigation solutions such as jamming and soft kill options. Their expertise allows seamless integration with broader C-UAS systems and third-party command and control software.

The Jaegar platform stands out for its pinpoint accuracy and high-speed capabilities, essential for detecting and tracking small targets at long ranges. This platform supports a variety of sensors, including long-range LWIR uncooled thermal sensors, MWIR cooled thermal sensors, and HD visible sensors, providing clear target verification and threat analysis. Advanced video tracking with auto-classification and AI capabilities ensures reliable performance in C-UAS applications.
Silent Sentinel’s extensive experience in the C-UAS market enables them to offer expert advice and integration services, ensuring optimal utilization of their EO systems. Their solutions are designed to meet the diverse needs and budgets of various missions, enhancing situational awareness and security in critical applications.
About MCA
MCA is one of the largest and most trusted integrators in the United States, offering world-class voice, data, and security solutions that enhance the quality, safety, and productivity of customers, operations, and lives. More than 65,000 customers trust MCA to provide carefully researched solutions for a safe, secure, and more efficient workplace. As your trusted advisor, we reduce the time and effort needed to research, install, and maintain the right solutions to make your workplace better.
Our team of certified professionals across the United States delivers a full suite of reliable technologies with a service-first approach. The MCA advantage is our extensive service portfolio to support the solution lifecycle from start to finish.


